Tracing phone numbers has evolved far beyond simply checking a caller ID. In cybersecurity, fraud detection, and investigative research, tools that dig deeper—uncovering details like carrier, country, and geolocation—have become essential. One such tool, PhoneInfoga, has gained popularity in open-source intelligence (OSINT) circles. It’s known for its ability to extract valuable metadata about phone numbers.
While it provides various insights, one of the most debated features is its ability to geolocate callers. Can a tool like PhoneInfoga reliably pinpoint a number’s origin on a map? Let’s dive into its mechanics, capabilities, and limitations to uncover the truth.
Understanding How PhoneInfoga Works
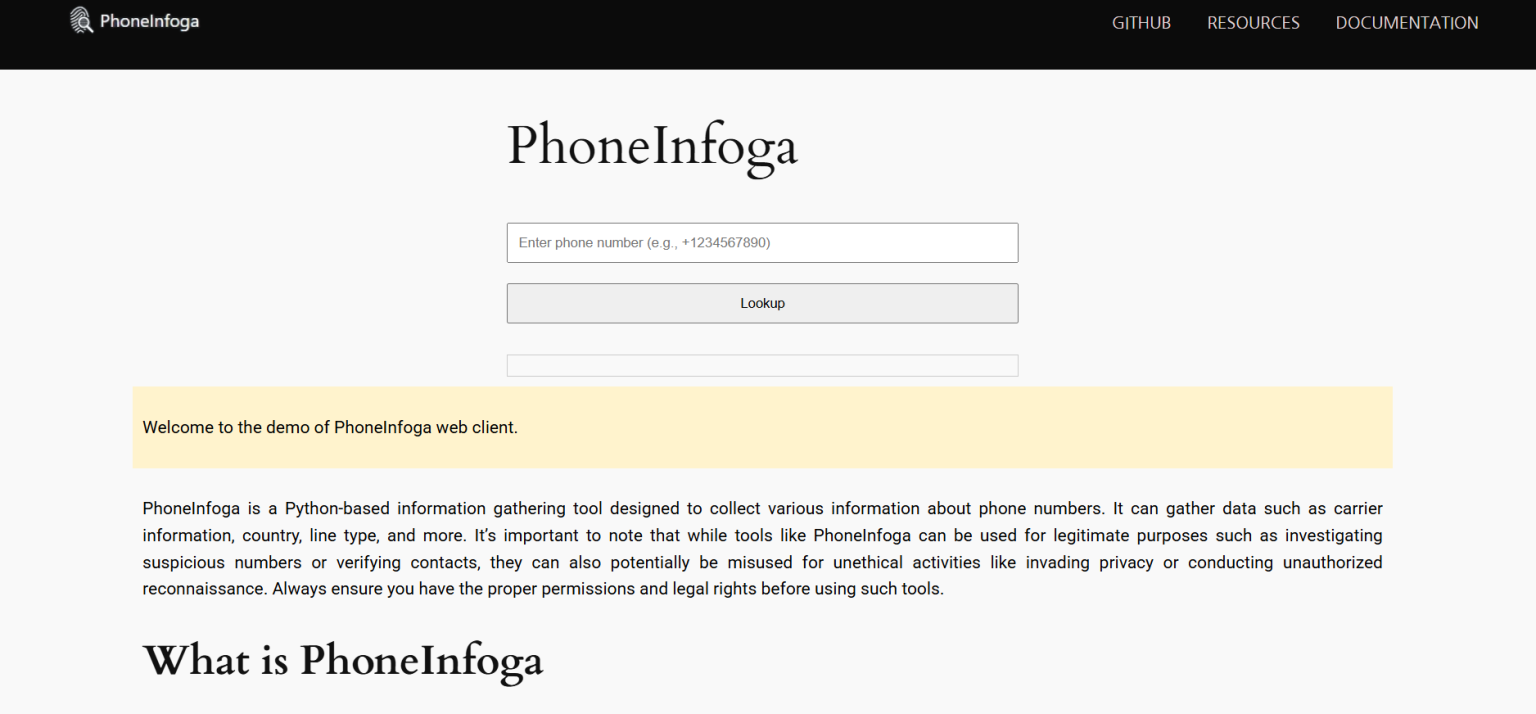
PhoneInfoga is an OSINT reconnaissance framework specifically built for gathering information on phone numbers. It’s an open-source project primarily used by security researchers, ethical hackers, and digital investigators. Developed using Python, it operates through a command-line interface and integrates with third-party services and databases to retrieve results.
Here’s what PhoneInfoga typically uncovers:
- Number validation and formatting
- Country and region of origin
- Carrier or telecom provider
- Line type (mobile, landline, VoIP)
- VOIP/virtual number detection
- Connected websites, social media traces
- Public breach of data or exposure
While these features are useful, geolocation remains a gray area. The idea of tracking a user’s exact location through a phone number is attractive, but not always technically or legally feasible.
Geolocation vs. Regional Information
It’s important to distinguish true geolocation from regional metadata. PhoneInfoga does not provide real-time, GPS-based tracking. Instead, it determines:
- The registered country and sometimes the city or area code
- Telecom region based on carrier data
- Any associated metadata suggesting location
In essence, PhoneInfoga narrows down a phone number to its likely origin, not the caller’s real-time position. This is a key limitation for those expecting live tracking capabilities.
How Geolocation Data Is Retrieved
PhoneInfoga uses multiple data sources and services to piece together geolocation-related details:
National Numbering Plans:
Every country has a unique phone numbering system. PhoneInfoga identifies the registered region by parsing number prefixes and area codes.
Carrier and Line Type Data:
Carriers often allocate number blocks to specific regions. While not exact, this data can suggest the number’s general location.
Third-Party APIs and Lookups:
PhoneInfoga can be configured to interact with services like Numverify, OVH, and other APIs. These services sometimes offer additional metadata that includes city-level or ISP-based data.
Social and Online Footprints:
If a number is tied to a user profile or exposed in a breach, PhoneInfoga can use that digital footprint to infer additional information.
However, none of these methods provides GPS-level geolocation. They function more like regional filters—useful, but not pinpoint-accurate.
Limitations of PhoneInfoga for Geolocating Callers
Despite its power, PhoneInfoga has critical limitations when it comes to accurate geolocation:
- No real-time tracking:
Unlike GPS or mobile tower triangulation, PhoneInfoga cannot track a caller’s live location. - Accuracy varies by country:
Some countries have detailed, publicly accessible telecom data. Others don’t. This affects location precision. - Dependence on external APIs:
The quality and availability of geolocation data depend heavily on third-party services used during scanning. - Inability to penetrate privacy layers:
Numbers hidden behind services like Google Voice or virtual numbers can’t be precisely geolocated.
For law enforcement or high-stakes investigations, PhoneInfoga may serve as an initial touchpoint, but it’s not a standalone geolocation tool.
Ethical and Legal Considerations
Attempting to geolocate individuals raises ethical and legal flags. PhoneInfoga, by design, does not violate privacy laws. It gathers data from public or semi-public sources and uses APIs with proper terms of service.
That said, users must be cautious:
- Avoid personal surveillance:
Using such tools for stalking, doxxing, or personal disputes is illegal in most jurisdictions. - Use for research or cybersecurity only:
The tool is best suited for verifying suspicious calls, gathering threat intel, or enhancing red team investigations. - Respect data laws:
Make sure any data pulled via PhoneInfoga adheres to GDPR, CCPA, or your country’s privacy framework.
PhoneInfoga should be part of a larger, legally compliant investigative workflow, not a solo solution for targeting individuals.
Use Cases Where PhoneInfoga Helps
Even with limited geolocation, PhoneInfoga offers significant utility across several domains:
Cybersecurity Investigations
Analysts use PhoneInfoga to verify scam calls or phishing numbers. Recognizing VOIP numbers or carriers associated with fraud rings adds context to threat detection.
OSINT Research
Digital investigators employ the tool to cross-check public data leaks or connect numbers with digital profiles. While not real-time, this can help triangulate suspect identities.
Enterprise Security
Companies use PhoneInfoga to identify spoofed or fraudulent calls received internally. It can flag anomalies, such as a local number with an offshore carrier.
Journalistic Verification
Reporters occasionally verify the legitimacy of tips or sources using tools like PhoneInfoga to avoid fake identities or phone-based deception.
In all these scenarios, PhoneInfoga doesn’t need real-time tracking. Its ability to narrow down possibilities makes it valuable.
Setting Up and Using PhoneInfoga
For users unfamiliar with command-line tools, getting started may seem daunting. However, the setup is fairly straightforward:
Installation Steps
Clone the GitHub Repository
Run:
- git clone https://github.com/sundowndev/PhoneInfoga.git
Navigate to the Directory
- cd PhoneInfoga
Install Requirements
- python3 -m pip install -r requirements.txt
Launch the Tool
- python3 phoneinfoga.py
Comparing PhoneInfoga to Other Tools
Other OSINT tools claim geolocation features, but many fall into similar limitations:
| Tool | Real-Time Location | Regional Metadata | OSINT Integration |
| PhoneInfoga | ❌ | ✅ | ✅ |
| Truecaller | ❌ | ✅ (Crowdsourced) | ❌ |
| Maltego | ❌ | ✅ | ✅ |
| Mobile Tracker | ✅ (If legal access) | ✅ | ❌ |
As shown, PhoneInfoga isn’t built for real-time GPS tracking but excels at OSINT-based metadata analysis.
Tips to Maximize Location Accuracy
While PhoneInfoga can’t provide exact coordinates, users can follow some strategies to improve regional accuracy:
- Use multiple APIs: Add API keys from providers like Numverify for enriched metadata.
- Combine with breach data tools: Tools like HaveIBeenPwned or Dehashed can tie a number to leaked profiles.
- Cross-reference social networks: Searching for the number in Google, Facebook, or LinkedIn sometimes surfaces location-tied posts.
- Leverage area code databases: Look up prefixes manually for context not covered by default PhoneInfoga scans.
In investigations, these steps form a chain of logic, not a single silver bullet. PhoneInfoga becomes powerful when used alongside other sources.
Conclusion
PhoneInfoga does not geolocate callers in real-time, nor does it offer exact pin drops like GPS trackers or law enforcement tools. However, it does offer reliable regional and carrier-level data, which can hint at a caller’s origin.
This tool won’t meet the needs of anyone expecting spy-level tracking. But for cybersecurity researchers, OSINT professionals, or anyone needing to validate phone numbers and gather surrounding data, PhoneInfoga remains a powerful resource.